Three Steps to Secure Your Social Media Accounts

Today, a typical internet user has dozens of passwords to keep safe.
1. Use Unique Passwords for Each Site.
The first thing hackers do when they've compromised a username and password from one site is try and log into a different site with the same details. The best way to avoid being compromised in this way is to choose long, complex passwords that are unique for each site.
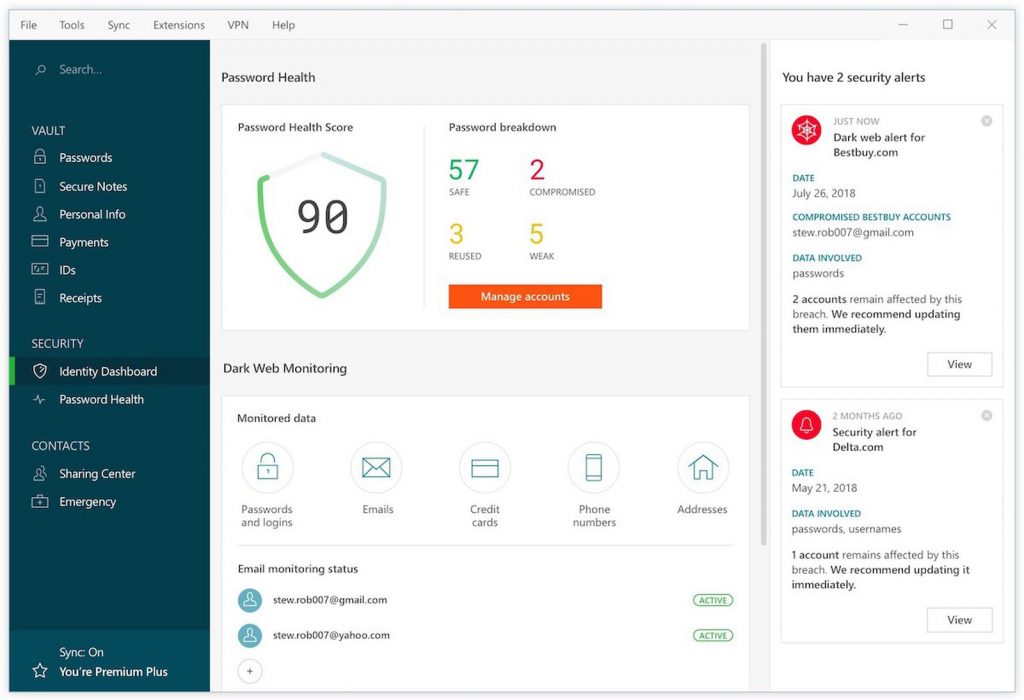
Sure, it can be a bit of a pain remembering lots of complex passwords but luckily, there's a solution for that. Password managers like Dashlane, Last Pass or 1Password will generate and store highly secure passwords for you.
2. Turn on 2-Factor Authentication
Even if you do pick a strong, unique password, usernames and passwords are still no longer considered secure. 2-Factor Authentication (2FA) or Multi-Factor Authentication (MFA) is a security technique that adds another method of proving your identify and dials up the security.
The additional factor could be anything from a range of options. Common second factors include:
- SMS One Time Codes - typically websites will send you a 5 or 6 digit code via SMS that you enter into the site or app.
- Authenticator Apps - by linking an authenticator app on your phone to your login you can get a 6-digit code from the app whenever you need to log into the website. This is generally considered much more secure than SMS, the most popular authenticator app is Google Authenticator but there are many options.
- Hardware Security Keys - a hardware based token, typically a USB key that contains a secure chip. Once linked, all you have to do is tap on the USB key and you're authenticated - it's that simple! A great example is the Open Source Nitrokey FIDO2 or the Yubikey range.
A great resource you can use to check which websites support two factor authentication is 2factorauth.org.
In Twitter you'd find this under Settings --> Account --> Login and security --> Security --> Two-factor authentication:

In Facebook it's under Settings --> Security and login --> Two-factor authentication:

In LinkedIn it's under Settings --> Sign in & Security --> Account access --> Two-step verification:

Here's what it looks like to setup in Instagram by going to Settings --> Privacy and Security --> Two-Factor Authentication:

3. Check Your Third Party Access
Over time you'll likely end up using Facebook apps, logging into sites with Facebook or Twitter, etc. Of course, the apps we use changes over time so this means that lots of apps you may not still use have access to your data. If any one of the apps you've connected gets breached you may find at best that they'd have access to your profile data or at worst they'd be able to use your profile to post scams and malware.
Thankfully, all of the big social media sites allow you to see which apps have been connected and in there you can remove access and revoke permissions for anything you're not using.
In Twitter go to Settings --> Data and permissions --> Apps and Sessions:

In LinkedIn go to Settings --> Data privacy --> Other applications:

In Facebook go to Settings --> Apps and Websites:

In Instagram go to Settings --> Apps and Websites:


